No products in the cart.
IoT Forensics - DVID Challenge (W53) - Digital Forensics Course Online
$219.00 – $499.00
Courses Included
Get the access to all our courses via Subscription
Subscribe
Product Description
This IoT Forensics course will explain IoT concepts, IoT construction, forensic assumptions and challenges, and the best approach to analyze an IoT system and an IoT environment (ex.: smart home). You will have access to an offline lab environment (using docker image) and an open-sourced IoT device: the DVID project. After your training, you will get into the device, be able to instrument the IoT environment by interacting with IoT systems, and collect logs and make a timeline of events for analysis.
COURSE BENEFITS
DURATION: 18 hours
CPE POINTS: On completion you get a certificate granting you 18 CPE points.
COMPLETE, SELF-PACED, PRERECORDED
Course format:
- Self-paced
- Pre-recorded
- Accessible even after you finish the course
- No preset deadlines
- Materials are video, labs, and text
- All videos captioned
After completing the course, you will be able to select the best technical and organizational approach for analyzing an IoT environment, both information stored in the device and event correlation from multiple IoT devices (ex.: smart home). Each student will be able to conduct an investigation without inadvertently compromising evidence.
This course targets:
- Investigators and analysts, to help them select the best approach about IoT forensics, especially if the device was used during a crime
- Security researchers, to help them identify misconfiguration in an IoT environment, for example, a smart house
- IT Decision makers, to help investigations in case of an incident like a virus compromised environment
IMPORTANT NOTE
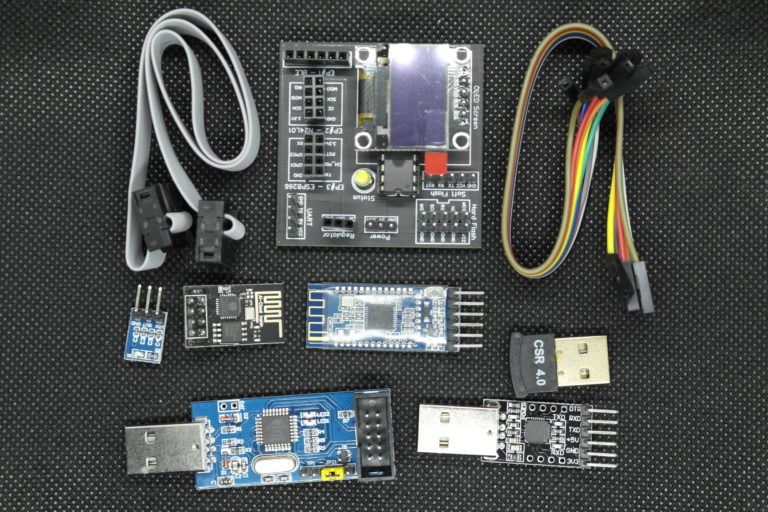
To fully participate in this course you need to have the DVID (Damn Vulnerable IoT Device). It is necessary to participate in the class. You can order one pre-made with this course, or manufacture one yourself - see instructions below.
BEFORE YOU START
The board is included in some course purchase options.
All practical work is based on a custom IoT device and a lab environment that simulates a smart house. The custom device is designed by the author and published on open-source. The main objective is to provide a physical device to improve IoT hacking/forensic skills and technical stored secret gathering using a forensic approach. More details about the board can be found on http://dvid.eu - if you want to produce it on your own, you will find all the necessary information there.
The board is composed of an Atmega328p chip and an OLED screen. Throughout the course, multiple firmware will be available: attendees will need to flash the corresponding firmware and start to hack and investigate.
The lab environment can be downloaded from a dedicated link. Based on docker containers, all runtime will be available from an OVA. This one can be instantiated with any virtualization software (ex.: VirtualBox or VMware). Detailed setup instructions will be provided.
This board is necessary to participate in the "IoT Forensics - DVID Challenge" online course. With some purchase options you'll get a pre-made, ready to go board.
The price includes international shipping, but it does not include any customs fees your country's Customs Office might charge. We are not responsible for getting your package through customs, and if your package is stopped at the border, you will be contacted by the Customs Office to make sure it goes through.
If you have the skills, you can purchase the standalone course (no DVID included), and using the open source schematic and component reference solder everything together. You are responsible for sourcing and financing all components and a naked board. The instructor can provide remote support throughout the process.
Premium subscriber? Order board only >>
Note about shipping
COVID-19: We are shipping normally. Due to restrictions, shipping time might be longer than usual, depending on the origin country. Please exercise all necessary caution when handling packages.
The packages will have tracking enabled, if they are shipped to the following countries: Germany, Saudi Arabia, Australia, Austria, Belgium, Brazil, Canada, South Korea, Croatia, Cyprus, Denmark, Spain, Estonia, United States, Finland, Gibraltar, Great Britain, Hong Kong, Hungary, Ireland, Iceland , Israel, Italy, Japan, Latvia, Lebanon, Lithuania, Luxembourg, Malaysia, Malta, Norway, New Zealand, Netherlands, Poland, Portugal, Russia, Singapore, Slovakia, Slovenia, Serbia, Sweden, Switzerland.
All packages going out to countries outside of this group will have tracking up to the point of arrival in the destination country.
As we have previously experienced issues with customs and delayed/lost packages when shipping to India, we will only be sending boards to India through a premium service (like DHL), which will include extra cost for you to cover.
- Basic knowledge of network, web and mobile security
- Basic knowledge about IoT hacking (W46 course is perfect)
- Knowledge of Linux OS
- Technical knowledge of programming - Python
- The DVID (either ordered pre-made here or made on your own; look below for details)
- Laptop with at least 50 GB free space
- 8GB minimum RAM (4GB for virtual machine/docker)
- External USB access (minimum of 2 USB ports)
- Administrative privileges on the system
- Docker-compatible operating system
During this course, all materials including slides, transcripts and fully detailed step by step instruction for training will be provided. During the lab, all runtime will be hosted on the attendee’s local machine using docker technology.
Time Organization
The course will be organized as shown in the following timetable. Estimated duration is 18 hours with 6 hours of practical work and 11 hours of lectures. The course will finish with an at home final challenge.
Module 1: Context and background
- Course time: 60 minutes
- Lab time estimation: 60 minutes
Module 2: Threat and forensic model
- Course time: 90 minutes
- Lab time estimation: 30 minutes
Module 3: IoT exploration
- Course time: 120 minutes
- Lab time estimation: 240 minutes
Module 4: Framework and tooling
- Course time: 90 minutes
- Lab time estimation: 90 minutes
Module 5: IoT Forensic analysis
- Course time: 180 minutes
- Lab time estimation: 120 minutes
Exam: Quiz (60 minutes)
Challenge: Let's play Cluedo
Extra time should be alotted for the final exam challenge. Your workload will depend on your skill level, but it will take at least a few hours to complete.
About the author: Arnaud Courty
 As an IoT expert, my main mission is to evangelise companies to take care of security from the design step.
As an IoT expert, my main mission is to evangelise companies to take care of security from the design step.
I work on internal and external offensive security analysis and assessment of security maturity of embedded systems upstream of their industrialization.
Since the beginning of IoT, I specialize in vulnerabilities research adapted to the embedded systems but also awareness of designers, developers and integrators. I take advantage of security events and working groups to campaign for a less vulnerable IoT world.
Course Syllabus
Module 1: Context and background
This module is designed to give basic knowledge about IoT Security and IoT Forensic technical background. After taking this module, you will be able to understand why IoT Forensics raises so many technical challenges and be ready to discover.
- Definitions: This part is designed to give all basic vocabulary in order to understand all modules of this course.
- IoT statistics: This part is designed to give an overview of the IoT market, understand why IoT offers hackers a huge attack surface in order to compromise systems for spying, sabotage or destruction.
- IoT Taxonomy & ecosystem: This part is designed to understand how an IoT system is built, the technologies used and the architecture. An ecosystem approach will help describe all forensic angles. Most of them will be explored in the rest of the course.
- IoT Forensic introduction: This part is designed to give you a first look into the forensic world. During this introduction, you will explore basic concepts, understanding main goals and constraints.
Lab setup
In this practical workshop, attendees will set up the lab environment to be sure all training is completed in the correct conditions.
First, play with lab environment
In this practical workshop, attendees will get hands-on with the lab environment. For example, they will interact with the simulated smart house by turning on the light or increasing the temperature. They will be able to see that each action generates logs and all of them can be analyzed into a dedicated SIEM.
Module 2: Threats and the forensic model
In this module, attendees will understand why and how forensic investigations occur in IoT. After talking about assumptions, this course will explore well-known IoT attacks where knowing forensic is a must-have to make a timeline and try to confuse a suspect. This module will also try to define a forensic model and enumerate all related challenges.
The last part of this module is about IoT device analysis. Students will learn how to analyze an unknown IoT device, try to collect technical information about alternate devices and crack into them.
- Forensic Assumptions: This part is designed to explain the basics of forensic analysis of IoT. By starting to retrieve sensitive information, many popular beliefs need to be clarified.
- Threats and well known IoT attacks: This part is designed to give an overview of main IoT attacks that have plagued the world. In each attack, this course will try to identify how attackers gain control, what the attack objectives are, and if a countermeasure is possible.
- Forensic approach: This part is designed to explore some technical and organizational approaches in order to conduct a forensic analysis, focused on IoT.
- Forensic challenges: This part is designed to understand what challenges forensics is trying to meet. For example, at least these topics will be covered:
- Complexity and diversity of IoT
- Cloud Forensics
- Limitation of IoT Device storage
- Securing the chain of custody
- Security issues
- Lack of forensics tools
- Multi jurisdictions
- Counter anti forensic mechanism
In this practical workshop, the attendee will enter the shoes of a detective in order to propose an investigation plan. Based on module materials, the attendee will need to think critically in order to choose the correct approach.
Module 3: IoT exploration
This module will cover IoT exploration in order to give enough knowledge to interact with the IoT ecosystem (hardware, short range and large range), to explore evidence and try to exfiltrate them. Well known protocols like UART or Bluetooth, Wifi, NFC, MQTT or HTTP API will be part of this module.
- Basics in IoT exploration: This part is designed to give you basic knowledge about protocols and the main concepts of IoT. The goal is to build a starting kit. For example, you will be able to read a datasheet or an FCC report to apprehend future explorations.
- Hardware exploration: This part is designed to explore hardware by understanding a PCB, identify possible read-only connections, try to dump embedded firmware and collect evidence for investigations. This part will not cover a full explanation of protocols, but will cover at least UART, SPI, I2C and JTAG.
- Short range exploration: This part is designed to explore short range protocols by understanding possible near interaction with hardware like Bluetooth, Zigbee, Z-Wave or NFC. This part will not cover a full explanation of protocols, but enough knowledge about what evidence may be found, where they are possibly located and find a stealthy way for exfiltration.
- Long range exploration: This part is designed to explore long range protocols by understanding possible large interaction with hardware like WiFi/LiFi, 6LowPAN/Thread, GSM, Sigfox/LoRa or CPL. This part will not cover a full explanation of protocols, but enough knowledge about what evidence may be found, where they are possibly located and find a stealthy way for exfiltration.
- Providers’ exploration: This part is designed to explore external providers, like Android, iPhone or Web content, to find possible evidence, where they are possibly located and find a stealthy way for exfiltration.
Hardware exploration
Attendees will interact with the lab environment on hardware to find as much evidence as possible for future investigation.
Short range exploration
Attendees will interact with the lab environment on short range protocols to find as much evidence as possible for future investigation.
Large range exploration
Attendees will interact with the lab environment on large range protocols to find as much evidence as possible for future investigation.
Provider exploration
Attendees will interact with the lab environment with Android, iPhone and Web providers to find as much evidence as possible for future investigation.
Module 4: Framework and tooling
This module is designed to give a working environment about forensics based on state-of-the-art forensic frameworks. From this knowledge, this module will explore well-known forensic tools with basic usage, tips and use cases.
- Use case exploration: This part is designed to give a technical approach on the four most representative use-cases:
- Unknown IoT device found on a crime scene (DVID)
- Crime committed by a drone
- Crime listened to by an Amazon Echo
- Crime committed in a smart house using OpenHAB
- Overview of existing frameworks: This part is designed to give a great understanding of all existing forensic frameworks in order to select the correct approach in all situations. This part will cover at least:
- Digital Forensic Investigation Framework for IoT (DFIF-IoT)
- Cloud-Centric Framework for Isolating Big Data (CFIBD-IoT)
- Forensic State Acquisition Controller (FSAC)
- Cloud based IoT Forensic toolkit (CIFT)
- Forensic Investigation Framework for IoT (FIF-IoT)
- Event-based evidence IoT Forensic Framework
- Big data Forensic Framework
- Drone Forensic Framework
- Fog-Based IoT Forensic Framework
- Integrated Digital Forensic Investigation Framework (IDFIF-IoT)
- Tooling: This part is designed to give you as much technical skill as possible in open-source tools. Some shareware tools will also be explored but only on the free functionalities. This part will cover at minimum:
- SIFT
- FTK
- Autopsy
- Plaso
- Volatility
Framework
Attendees will complete their investigation plan using framework knowledge to be sure that no evidence was forgotten.
Tooling
Attendees will use SIFT, Plaso and Volatility to explore samples from crime scenes.
Module 5: IoT Forensic analysis
This module is designed to give all knowledge about conducting a forensic investigation, especially from evidence identification, data extraction, interpretation, analysis, secured storage and reporting.
- Forensic Acts and Laws: This part is designed to give a quick overview of worldwide Forensic Acts and Laws.
- Planning and preparation: This part is designed to cover the investigation preparation process including audit trail, organization, protecting evidence and managing errors.
- Evidence identification: This part is designed to help attendees identify evidence from multiple sources (ex.: type of evidence, reading tools or default location).
- Evidence collection and secured storage: This part is designed to help attendees extract evidence from an identified source of data (ex.: device wiring, cloud extraction) and store them in a secure way.
- Reporting: This part is designed to give writing tips to create a relevant report.
- Doing investigation: This part is designed to give a fully detailed methodology to conduct a real investigation from collection, analysis, and secure storage to reporting.
Attendees will take all materials from previous practical work (investigation plan, framework and IoT hacking skills) to process a real investigation. In the simulated smart house, they will explore a network and smart devices to retrieve as much evidence as possible to resolve the crime scene. The result of this training will be an investigation report.
Exam: Audit an IoT device
Exam: Quiz
The exam for this course is a quiz composed of 60 questions. All questions are based on course materials. In order to pass this exam, 40 correct answers are required.
Challenge: Let's play Cluedo
Every one of you know the most famous murder mystery game Cluedo, or Clue. During this challenge, you will be a security consultant and take part in the investigation to determine who murdered the victim, where the crime took place and which weapon was used. From analyzing all IoT devices found in the house, you will lead the investigation and report all your conclusions to your upper hierarchy.
This challenge result should be a fully detailed investigation report, including the attack timeline and, at least, the murder, the location and the weapon. All findings and evidence must be collected and well associated with an explanation. In order to improve yourself, a correction of your report can be done by the author.
Contact:
If you have any questions, please contact us at [email protected].
FAQ
ABOUT THE DVID:
The DVID (Damn Vulnerable IoT Device) is an intentionally vulnerable IoT device to help you learn about IoT security.
Yes. Without it you won’t be able to do any practical work throughout the course, a big part of the content will refer directly to it as well.
You can order a premade device with us, or you can make one yourself (buy all components and solder them together). For all instructions see the course description.
The DVID is manufactured by the instructor of the course, Arnaud Courty.
Yes. All boards are thoroughly tested before shipping, as well as all components and attack tools provided with the device.
No, we don’t offer part-only packages for retail customers. It is possible for group orders - see “Special orders” section.
SHIPPING:
Shipping will be done worldwide, but tracking will be available only for specific countries.
The packages will have tracking enabled, if they are shipped to the following countries: Germany, Saudi Arabia, Australia, Austria, Belgium, Brazil, Canada, South Korea, Croatia, Cyprus, Denmark, Spain, Estonia, United States, Finland, Gibraltar, Great Britain, Hong Kong, Hungary, Ireland, Iceland , Israel, Italy, Japan, Latvia, Lebanon, Lithuania, Luxembourg, Malaysia, Malta, Norway, New Zealand, Netherlands, Poland, Portugal, Russia, Singapore, Slovakia, Slovenia, Serbia, Sweden, Switzerland.
All packages going out to countries outside of this group will have tracking up to the point of arrival in the destination country.
We have previously experienced issues with customs and delayed/lost packages when shipping to India. For this reason, if you want to order the board, we will only be sending it through a premium service (like DHL), which will include extra cost for you to cover.
We will be contacting you by email with further instructions.
Since the boards are manufactured just for this course, we will contact you with specific details. You will be notified when the shipment is made. We do our best to send packages within 7 days of ordering.
Please document the package and contact our e-Learning manager at [email protected]
Please document the board and contact our e-Learning manager at [email protected]
If you received a notice from us confirming that we’ve sent the package and the shipment does not arrive after a reasonable amount of time, please contact our e-Learning Manager at [email protected]
I AM A HAKIN9 PREMIUM SUBSCRIBER / IT PACK PREMIUM SUBSCRIBER / LIFETIME SUBSCRIBER
Yes, the course is included in your subscription, but the board is not. Don’t worry, we have a special product made just for you, where you can purchase the pre-made board independently from the course: https://eforensicsmag.com/product/board-only-dvid-challenge-w53/ You can also manufacture the board yourself, if you’re feeling up to it - see instructions in the course description.
No. The BOARD ONLY product includes only the pre-made board and course access is not included. You have course access through your premium subscription.
No, you should either purchase a seat on the course, or renew your subscription.
Yes, you will be able to view the training materials and see the assignments. However, you won’t be able to perform any practical exercises from the course, unless you make the board yourself (instructions provided in the course description).
SPECIAL ORDERS
My University would be interested in enrolling our students in this course. Are there any discounts?
Educational institutions receive a discount for course enrollment. The price of the DVIDs (if you choose to order them as well) will not be discounted. Please contact Joanna Kretowicz at [email protected] for further details.
You can make a bulk order, but the price will not be discounted - the price of the DVID as offered on the website includes bare manufacturing and shipping costs. Please contact Joanna Kretowicz at [email protected] for further details.
Yes, provided you meet certain criteria in regards to the amount of the packages you want. Please contact our Product Manager Marta Sienicka at [email protected] for further details.
Companies receive a discount for group course enrollment only. The price of the DVID (if you choose to order it as well) will not be discounted. Please contact Joanna Kretowicz at [email protected] for further details.
You can make a bulk order, but the price will not be discounted - the price of the DVID as offered on the website includes bare manufacturing and shipping costs. Please contact Joanna Kretowicz at [email protected] further details.
Yes, provided you meet certain criteria in regards to the amount of complete packages you want. Please contact Joanna Kretowicz at [email protected] for further details.
RETURNS & REFUNDS
Please document the package and please contact our e-Learning Manager at [email protected]. We offer replacements if you meet the criteria for one.
Please document the board and contact our e-Learning Manager at [email protected]. We offer replacements if you meet the criteria for one.
You can only return undamaged boards within 14 days of receiving them. You have to inform us of your intent to return within that time frame, by email at [email protected] You are responsible for the return shipment and its cost. It should be made to a return address we provide. You must provide us with proof of shipment within 7 days of informing us of intent to return. After we receive your return package, the board will be evaluated for damage, and if everything checks out, we’ll reverse your payment.
Yes. You can only return undamaged boards within 14 days of receiving them. You have to inform us of your intent to return within that time frame, by email at [email protected]. You are responsible for the return shipment and its cost. It should be made to a return address we provide. After we receive your return package, the board will be evaluated for damage, and if everything checks out, we’ll reverse your payment.
Yes, if you meet the criteria. For our return policy for online courses, please refer to our Terms of Service.
Yes, if you meet the criteria. For our return policy for online courses, please refer to our Terms of Service.
Only logged in customers who have purchased this product may leave a review.
FAQ
ABOUT THE DVID:
The DVID (Damn Vulnerable IoT Device) is an intentionally vulnerable IoT device to help you learn about IoT security.
Yes. Without it you won’t be able to do any practical work throughout the course, a big part of the content will refer directly to it as well.
You can order a premade device with us, or you can make one yourself (buy all components and solder them together). For all instructions see the course description.
The DVID is manufactured by the instructor of the course, Arnaud Courty.
Yes. All boards are thoroughly tested before shipping, as well as all components and attack tools provided with the device.
No, we don’t offer part-only packages for retail customers. It is possible for group orders - see “Special orders” section.
SHIPPING:
Shipping will be done worldwide, but tracking will be available only for specific countries.
The packages will have tracking enabled, if they are shipped to the following countries: Germany, Saudi Arabia, Australia, Austria, Belgium, Brazil, Canada, South Korea, Croatia, Cyprus, Denmark, Spain, Estonia, United States, Finland, Gibraltar, Great Britain, Hong Kong, Hungary, Ireland, Iceland , Israel, Italy, Japan, Latvia, Lebanon, Lithuania, Luxembourg, Malaysia, Malta, Norway, New Zealand, Netherlands, Poland, Portugal, Russia, Singapore, Slovakia, Slovenia, Serbia, Sweden, Switzerland.
All packages going out to countries outside of this group will have tracking up to the point of arrival in the destination country.
We have previously experienced issues with customs and delayed/lost packages when shipping to India. For this reason, if you want to order the board, we will only be sending it through a premium service (like DHL), which will include extra cost for you to cover.
We will be contacting you by email with further instructions.
Since the boards are manufactured just for this course, we will contact you with specific details. You will be notified when the shipment is made. We do our best to send packages within 7 days of ordering.
Please document the package and contact our e-Learning manager Marta at [email protected]
Please document the board and contact our e-Learning manager Marta at [email protected]
If you received a notice from us confirming that we’ve sent the package and the shipment does not arrive after a reasonable amount of time, please contact our e-Learning Manager Marta at [email protected]
I AM A HAKIN9 PREMIUM SUBSCRIBER / IT PACK PREMIUM SUBSCRIBER / LIFETIME SUBSCRIBER
Yes, the course is included in your subscription, but the board is not. Don’t worry, we have a special product made just for you, where you can purchase the pre-made board independently from the course: https://eforensicsmag.com/product/board-only-dvid-challenge-w53/ You can also manufacture the board yourself, if you’re feeling up to it - see instructions in the course description.
No. The BOARD ONLY product includes only the pre-made board and course access is not included. You have course access through your premium subscription.
No, you should either purchase a seat on the course, or renew your subscription.
Yes, you will be able to view the training materials and see the assignments. However, you won’t be able to perform any practical exercises from the course, unless you make the board yourself (instructions provided in the course description).
SPECIAL ORDERS
My University would be interested in enrolling our students in this course. Are there any discounts?
Educational institutions receive a discount for course enrollment. The price of the DVIDs (if you choose to order them as well) will not be discounted. Please contact Joanna Kretowicz at [email protected] for further details.
You can make a bulk order, but the price will not be discounted - the price of the DVID as offered on the website includes bare manufacturing and shipping costs. Please contact Joanna Kretowicz at [email protected] for further details.
Yes, provided you meet certain criteria in regards to the amount of the packages you want. Please contact our Product Manager Marta Sienicka at [email protected] for further details.
Companies receive a discount for group course enrollment only. The price of the DVID (if you choose to order it as well) will not be discounted. Please contact Joanna Kretowicz at [email protected] for further details.
You can make a bulk order, but the price will not be discounted - the price of the DVID as offered on the website includes bare manufacturing and shipping costs. Please contact Joanna Kretowicz at [email protected] further details.
Yes, provided you meet certain criteria in regards to the amount of complete packages you want. Please contact Joanna Kretowicz at [email protected] for further details.
RETURNS & REFUNDS
Please document the package and please contact our e-Learning Manager Marta at [email protected]. We offer replacements if you meet the criteria for one.
Please document the board and contact our e-Learning Manager Marta at [email protected]. We offer replacements if you meet the criteria for one.
You can only return undamaged boards within 14 days of receiving them. You have to inform us of your intent to return within that time frame, by email at [email protected] You are responsible for the return shipment and its cost. It should be made to a return address we provide. You must provide us with proof of shipment within 7 days of informing us of intent to return. After we receive your return package, the board will be evaluated for damage, and if everything checks out, we’ll reverse your payment.
Yes. You can only return undamaged boards within 14 days of receiving them. You have to inform us of your intent to return within that time frame, by email at [email protected]. You are responsible for the return shipment and its cost. It should be made to a return address we provide. After we receive your return package, the board will be evaluated for damage, and if everything checks out, we’ll reverse your payment.
Yes, if you meet the criteria. For our return policy for online courses, please refer to our Terms of Service.
Yes, if you meet the criteria. For our return policy for online courses, please refer to our Terms of Service.




Reviews
There are no reviews yet.