No products in the cart.
Requested resource is not accessible
The access to this course is restricted to eForensics Premium or IT Pack Premium Subscription
Course duration: 18 hours (18 CPE points)
Self-paced, pre-recorded
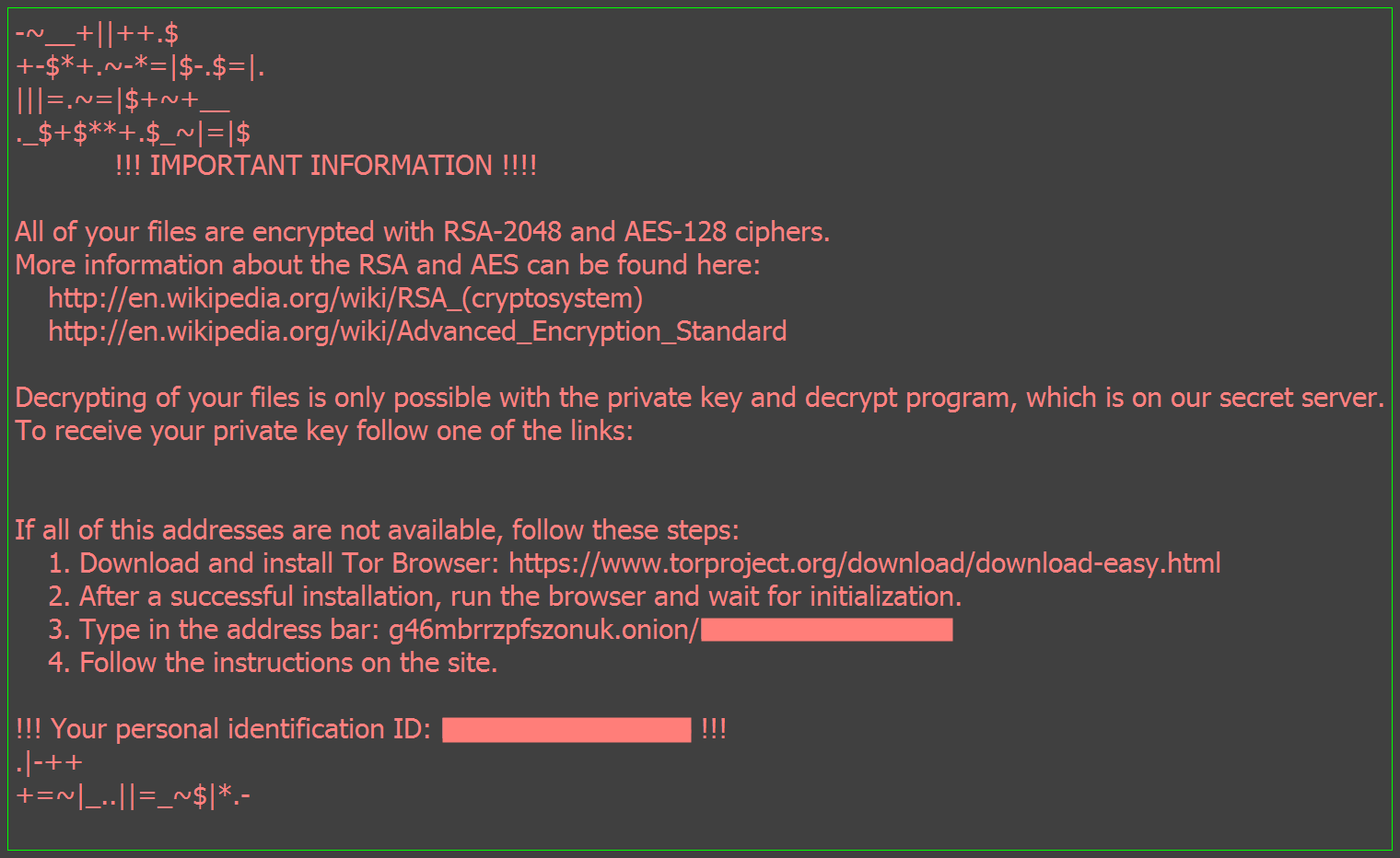
This is a forensic course. First of all, we are interested in understanding how ransomware works, not only in “external” results (like a blocked screen), but in internal properties (in other words, the cipher properties, the payload procedure and the vector). Below, we have just one of a million of Locky blocker screen wallpaper template.
There are so many questions that we can ask about ransomware, but the main forensics questions (in my opinion) are:
- What is the pattern behavior behind ransomware file encryption?
- What are the ransomware file properties?
- What is the evidence in file format, size, libraries, functions and calls procedures?
These questions are raised because when we read about how the ransomware attacks have been stopped, we see a mix of technical approach and a sum of lucky action. And, faced with this scenario, we keeping search for answers!
People say that forensic science is a “day after” science (oh, ok, I hear this in my class...). But, this narrow view compromises the understanding of how digital forensics can contribute to malware analysis.
In some perspectives, malware analysis “is an art” because it brings together certain skills (like reverse engineering) that should be used together to understand the features of the infection and find solutions that will protect victims in the future. If we look closely at an impressionist picture, we can not see the composition as a whole, the color combinations defining the scales and the millions of shades upon hues will be lost by our gaze. But if we take two steps back, the composition is revealed in all its magnitude! Malware analysis and, especially, ransomware analysis, works that way.
Ransomware was not born in the last five years... there are artifacts from more than two decades of stolen data. Of course, with the latest events in the media, we could see the evolution of the examples: a well-crafted cryptographic key, delivery through cybernetic currency, exploitation of TOR services, interchange among groups, etc. If we look from an appropriate distance, we can see these details.
In this course, we will try to see the whole composition. This course attempts to study ransomware artifacts. Since the course has a forensics perspective, we will not develop ransomware, but analyze as much as possible of the extracted evidence from pieces or virtual machines.
In the labs, when we analyze an infected host, we will use VMware to capture memory dump (.vmem file).
What will you learn?
- The students will learn to analyze the infected host (running in virtual machine) and the entropic file rate using memory ,vmem dumped file.
- Analyzing extracted .dmp files using radare2.
- Forensics analysis of network evidence.
- Forensics analysis of memory dump using Volatility.
- System image analysis using Bulk_Extractor and/or Scalpel.
- Windows analysis using Sysinternals.
What skills will you gain?
- Students gain skills in reverse engineering and malware behavior.
- Analyze memory dumps.
- Extract evidences in TOR channel.
- Analyze system infections.
- Analyze extracted files.
- Retrieving cyphers.
- Extracting and analyzing executable files from memory image.
What will you need?
- This course requires a Linux environment to analyze the artifacts. I will use Kali Linux running on ASUS notebook (RAM: 8 GB & 1 TB HD). In my case, I am using my own notebook to perform the analysis (but you can use Kali Linux in a virtual machine). My notebook runs UBUNTU 1604 LTS. I just install the tools that I need.
- Assembly knowledge.
- C and C++ knowledge basic programming security safety practices (PSSP).
What should you know before you join?
- This course requires Volatility and Rekall usage knowledge.
- This course requires C and C++ programming knowledge.
- Basic assembly knowledge.
- Registers, CPU, looping
- Network TCP protocol.
- Cryptographic basic knowledge.
Your intructor: Paulo Henrique Pereira, PhD
 I was born in São Paulo, the big, boring and bestial industrial city of my country, Brazil. I obtained my PhD at São Paulo University (USP) in analytical induction, a math, logic, statistical and philosophic area. I never work in this area...but, one day, walking on a Sunday morning, I discovered that I could use my statistical skills to analyze malware behavior, like a math model. So, I invested my time in this area since 1989.
I was born in São Paulo, the big, boring and bestial industrial city of my country, Brazil. I obtained my PhD at São Paulo University (USP) in analytical induction, a math, logic, statistical and philosophic area. I never work in this area...but, one day, walking on a Sunday morning, I discovered that I could use my statistical skills to analyze malware behavior, like a math model. So, I invested my time in this area since 1989.
Nowadays, I teach forensics at the University Nove de Julho (UNINOVE) and I work with forensic analysis and malware analysis (reverse engineering of malware) as a free consultant. To escape from reality, in my spare time, I go to some place to practice fly fishing in the rivers that cut through the mountains and I keep going to programming in C and Python my own pieces of software.
Course format:
- The course is self-paced – you can visit the training whenever you want and your content will be there.
- Once you’re in, you keep access forever, even when you finish the course.
- There are no deadlines, except for the ones you set for yourself.
- We designed the course so that a diligent student will need about 18 hours of work to complete the training.
- The course contains video and text materials, accompanied by practical labs and exercises.
Syllabus
Module I: RAAS Wannacry Family.
This module covers the Wannacry ransomware in forensics perspectives, trying to analyze its polymorphism properties and functionality. The Wannacry family has many variations and uses not only one vector to spread in the system. As much as possible, we will try to discover the behavior of the executable file that we use in the lab.
Covered topics:
- RAAS forensics.
- System infection analysis.
- Memory analysis.
Exercises:
- Laboratories to analyze memory dump.
- Practical laboratories and exercises involving the RAAS.
- Exploring W10 Enterprise security schemes and ransomware infection.
- Extracting and analyzing executable files from memory image.
Module II: TOR forensics.
What network traffic is used by ransomware? Ransomware artifact attacks are using TOR encrypted connection to distribute the ransomware. In this module, we will try analyzing the TOR ransomware connection repository. What will TOR network artifacts reveal? What will TOR network artifacts reveal?
Covered topics:
- TOR possible evidence.
- Memory analysis.
Exercises:
- Practical laboratories to extract evidence in TOR channel.
- TOR links procedure.
- Wannacry TOR calls.
Module III: Cypher forensics.
Since cryptography is the key vector behavior of ransomware, the ransomware cyphers are the main properties to unlock files. This module will try to apply the forensics tools to understand the implementation of the cypher vector.
Covered topics:
- Cyphering order objects in Windows system.
- Memory analysis.
Exercises:
- Reversing @decriptor using radare2.
- Retrieving cyphers.
Module IV: Cryptowall family.
Digital forensic investigation is a science that works with pieces of evidence trying to mount an entire picture of an attack. In this module, will use reverse engineering to analyze Cryptowall artifacts.
Covered topics:
- Reverse engineering analysis.
- Extracted file analysis.
- Memory analysis.
Exercises:
- Laboratories to analyze system infection.
- Laboratories to analyze extracted files.
- Wannacry infection modules in W7 SP1 x86.
Recommended reading: LISKA, A. & GALLO, T. Ransomware: Defending Against Digital Extortion. London: Elsevier, 2016.
Contact:
If you have any questions, please contact us at [email protected].

Very informative course
The course itself was very informative and dealt with the ins and outs of Memory Forensics for Ransomware. The instructor was knowledgeable and knew his subject matter. I would also like to thank Marta for her assistance and feedback!
The only thing I would say that needs to be worked on is the instructor’s has a very heavy accent and at times it was difficult to understand him, he would have a tendency to pause with Umms and Ahhs, which too made it difficult at times to understand. May I suggest a written transcript of the presentation be included for better comprehension.
Overall, very satisfied and plan on taking another course with them.