No products in the cart.
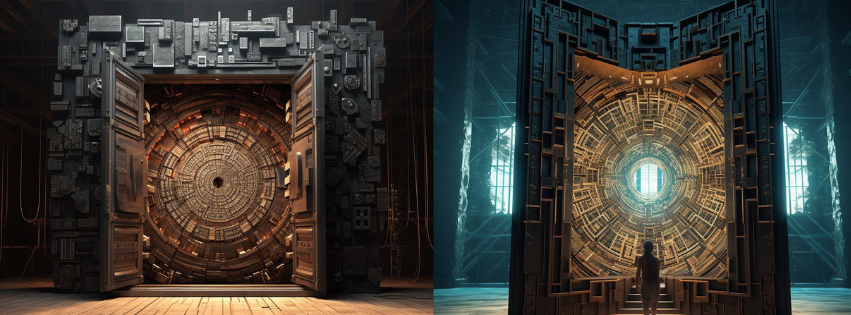
Known Fraudulent Methods that Adopt New Techniques to Overcome Protection Barriers and Violate Information Security GEORGE CHRISTOPHER ROCIO In recent years, we have noticed an increase in the number of crimes in which criminal agents use increasingly sophisticated mechanisms to break the security barrier related to authentication processes. This article....
Subscribe
Login
0 Comments
