No products in the cart.
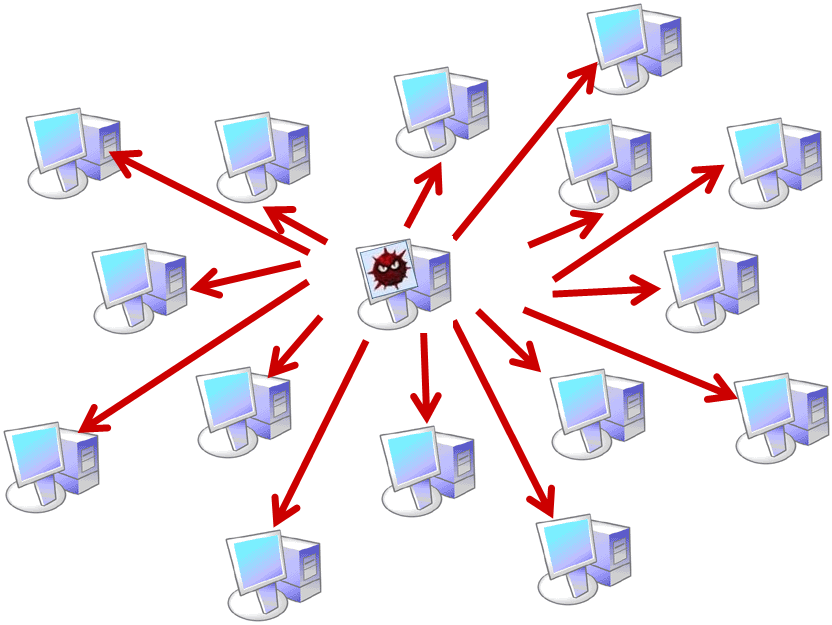
Looking into the world of security there are many attack vectors with respect to validations of the input in the wild. It is more prominent in the world of Web Applications but with respect to the infrastructure each and every thing which accepts an input is surrounded by a....
Author
Latest Articles
 Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn
Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn BlogJuly 11, 2017For the Love of The Game by Jessica Gulick
BlogJuly 11, 2017For the Love of The Game by Jessica Gulick BlogJune 29, 2016Finding Advanced Malware Using Volatility
BlogJune 29, 2016Finding Advanced Malware Using Volatility BlogJuly 3, 2015Banana Pi Pro - Review
BlogJuly 3, 2015Banana Pi Pro - Review
[…] vector is a path or means through which a hacker gains access to your digital content,” says Amit Kumar Sharma. Here are potential school district attack […]
Good article
togel singapore