No products in the cart.
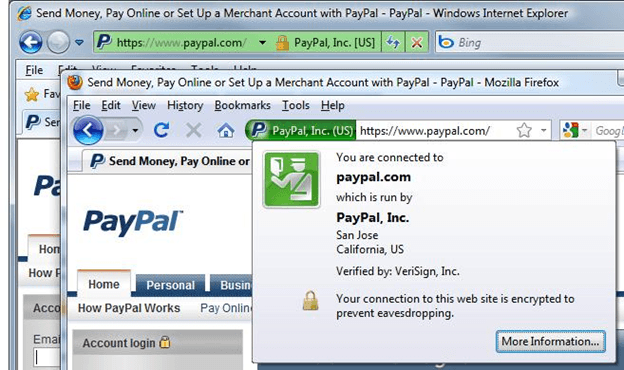
Dennis Chow, MBA Senior Information Security Engineer This article demonstrates how users can still be susceptible to their secure connections being monitored or modified without their knowledge on-the-fly with a device that a malicious person can put into the network. Legitimate use cases can be for troubleshooting or basic traffic monitoring....
Author
Latest Articles
 Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn
Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn BlogJuly 11, 2017For the Love of The Game by Jessica Gulick
BlogJuly 11, 2017For the Love of The Game by Jessica Gulick BlogJune 29, 2016Finding Advanced Malware Using Volatility
BlogJune 29, 2016Finding Advanced Malware Using Volatility BlogJuly 3, 2015Banana Pi Pro - Review
BlogJuly 3, 2015Banana Pi Pro - Review
Subscribe
Login
0 Comments