No products in the cart.
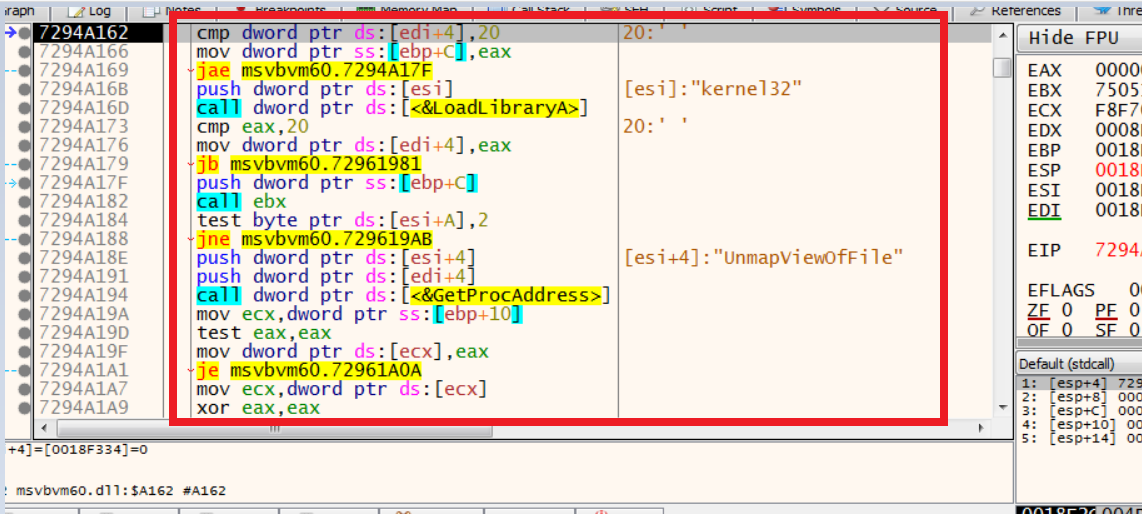
Debugging VisualBasic Malware Introduction Reversing malware written in Visual Basic has always been a challenge, or nightmare, as its functionality is totally different from other malware. Malware written in C, C++ (which we mostly see in our day-to-day reversing) mostly gets compiled directly into standard machine instructions that, when we....
Author
Latest Articles
 BlogSeptember 29, 2020Using the Google custom search engine for OSINT | By Maciej Makowski
BlogSeptember 29, 2020Using the Google custom search engine for OSINT | By Maciej Makowski BlogSeptember 22, 2020Sysmon 12.0 — EventID 24 | By Olaf Hartong
BlogSeptember 22, 2020Sysmon 12.0 — EventID 24 | By Olaf Hartong BlogSeptember 21, 2020Decrypting Databases Using RAM Dump – Health Data | By Michal Rozin
BlogSeptember 21, 2020Decrypting Databases Using RAM Dump – Health Data | By Michal Rozin BlogSeptember 18, 2020TikTok — Using OSINT to Discover New Leads | By Josh Richards
BlogSeptember 18, 2020TikTok — Using OSINT to Discover New Leads | By Josh Richards
what an analysis!!! simply amazing!