No products in the cart.
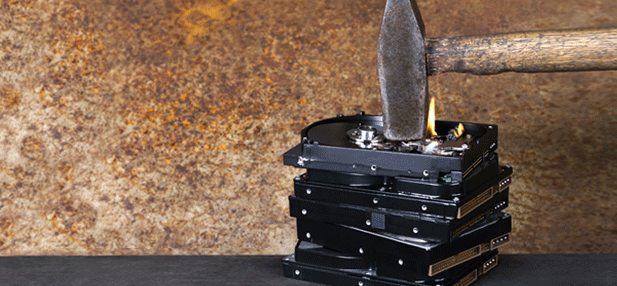
by Mark Garnett What you will learn: Forensic imaging techniques MFT file structure MFT file entry recovery How people attempt to hide and/or delete data The importance of file system metadata What you should know: Basic forensic data acquisition methodologies File signature analysis Investigative techniques Data recovery With the advent....
Author
Latest Articles
 Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn
Our AuthorsFebruary 19, 2018Meet our expert - Cordny Nederkoorn BlogJuly 11, 2017For the Love of The Game by Jessica Gulick
BlogJuly 11, 2017For the Love of The Game by Jessica Gulick BlogJune 29, 2016Finding Advanced Malware Using Volatility
BlogJune 29, 2016Finding Advanced Malware Using Volatility BlogJuly 3, 2015Banana Pi Pro - Review
BlogJuly 3, 2015Banana Pi Pro - Review